Secure Networking Solutions
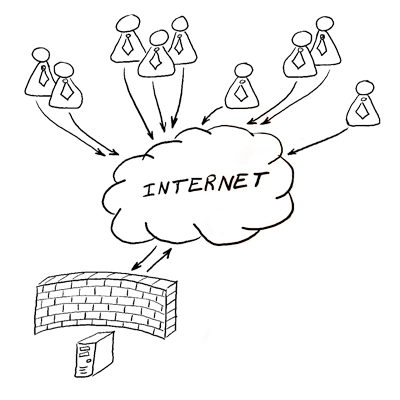
Virtual Private Network - VPN - has attracted the attention of many organizations looking to both expand their networking capabilities and reduce their costs.
A virtual private network (VPN) is a network that uses a public telecommunication infrastructure, such as the Internet, to provide remote offices or individual users with secure access to their organization's network. A virtual private network can be contrasted with an expensive system of owned or leased lines that can only be used by one organization. The goal of a VPN is to provide the organization with the same capabilities, but at a much lower cost.
A VPN works by using the shared public infrastructure while maintaining privacy through security procedures and tunneling protocols such as the Layer Two Tunneling Protocol (L2TP). In effect, the protocols, by encrypting data at the sending end and decrypting it at the receiving end, send the data through a "tunnel" that cannot be "entered" by data that is not properly encrypted. An additional level of security involves encrypting not only the data, but also the originating and receiving network addresses.
We provide four types of VPN Service
- The Point-to-Point Tunneling Protocol (PPTP) encapsulates Point-to-Point Protocol (PPP) frames into IP datagram’s for transmission over an IP-based internetwork. TCP connection is used for tunnel maintenance and GRE is used to encapsulate PPP frames for tunneled data. User name and password are used for authentication.
- Layer Two Tunneling Protocol (L2TP) is a combination of PPTP and Layer 2 Forwarding (L2F) protocols. L2TP uses UDP messages over IP internet works for both tunnel maintenance and tunneled data. User name and password are used for tunnel authentication.
- IPSec provides a mechanism for secure data transmission over IP network, ensuring confidentiality, integrity, and authenticity of data communications over unprotected networks such as the Internet.
- SSL VPN (Secure Sockets Layer Virtual Private Network) is a kind of VPN that runs on Secure Socket Layers technology and is accessible via HTTPS over web browsers. SSL functions between the TCP layer and application layer protocols. Corporate users are able to access confidential applications or shared files on standard web browsers. The main benefit of SSL VPN technology is that because it is user-based, not device-based, any authorized user can login from web-enabled PC’s for secure, remote access of confidential files.
VPN solutions
- Remote Access: Remote access VPN connection is made by a remote access client, or a single user computer, that connects to a private network.
- Site-to-Site: LAN-to-LAN VPN connection is made by two routers to connect two portions of private networks.